No Major Cyber Incidents in FY 2018, Says OMB: This Is IT
Steps that federal agencies are taking to thwart attacks on government computer systems appear to be paying off.
The Office of Management and Budget’s Federal information Security Modernization Act (FISMA) fiscal2018 Annual Report to Congress reports no “major incidents” last year, despite 31,107 incidents overall.
According to OMB, a major incident is a computer breach that is either likely to cause demonstrable harm to national interests or that involves unauthorized access to personally identifiable information (PII). Any unauthorized access to the PII of 100,000 or more people is automatically classified as major.
What’s Working
The OMB credits the reduction of major incidents to a combination of aggressive technological and administrative moves across the government. For example, 70 out of 102 federal agencies have now implemented all three EINSTEIN intrusion prevention systems, including the 24 agencies covered by the CFO Act, which mandates improved financial management. EINSTEIN is the Homeland Security Department’s common shared detection and warning system for breaches. As part of the implementation of DHS’s Continuous Diagnostics and Mitigation (CDM) program, all CFO agencies are also reporting threat data in near-real time to their respective agency dashboards using CDM Phase 1 asset management tools.
These successes are a result of emphasis on several core cyber priorities, including: providing greater protections for high-value assets; increasing cybersecurity threat awareness; standardizing cybersecurity and IT capabilities across agencies; enhancing the maturity of security operations centers; and holding senior agency cybersecurity officials accountable.
The report highlights in particular the success agencies have had translating cybersecurity spending into improved security.
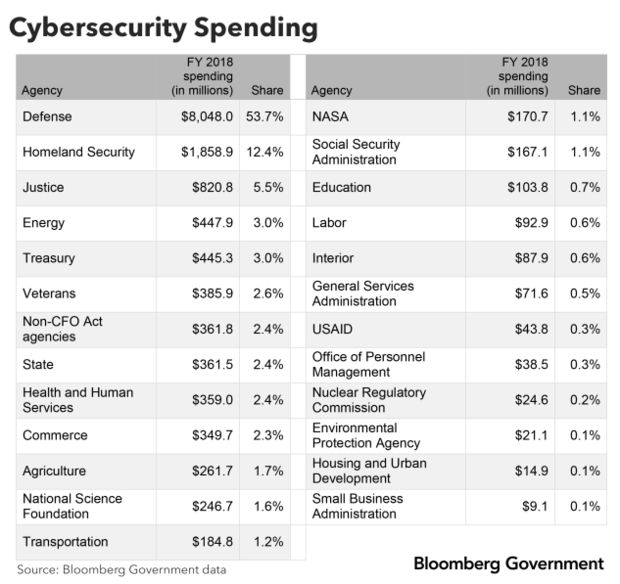
OMB reports that fiscal 2018 federal cybersecurity spending totaled $15 billion, with the Defense Department ($8 billion in obligations), DHS ($1.9 billion), and Justice Department ($821 million) accounting for 72 percent of the total.
After “other/unknown,” most cybersecurity incidents were caused by “improper usage” (9,674), email/phishing (6,930) and attacks executed from web-based applications (3,332), according to the report.
Some cyber gaps remain. For example, only 67 percent of CFO Act agencies and 54 percent of non-CFO agencies maintain programs for agencywide continuous privacy monitoring programs. The report indicates that no CFO agencies and only 8% of non-CFO agencies take adequate steps to protect federal information accessed through contracts and other agreements.
Looking Ahead
BGOV is currently tracking more than $18 billion in cybersecurity contracts ending on or after Jan. 1, 2020. The largest cyber contract vehicles for recompetes include the General Services Administration’s IT Schedule 70 ($2 billion), NASA’s Solutions for Enterprise-Wide Procurement V (SEWP V, $1.6 billion) and DOD’s Next Generation Enterprise Network (NGEN, $1.6 billion).
BGOV’s solicitation search also lists 1,586 new cybersecurity opportunities in the pre-RFP and RFP stages.
To contact the analyst: Paul Murphy in Washington at pmurphy@bgov.com
To contact the editors responsible for this story: Daniel Snyder at dsnyder@bgov.com; Jodie Morris at jmorris@bgov.com